Mission-critical applications are software that keep hospital networks alive, financial systems solvent, power grids operational, and defense infrastructure coordinated. However, they have become the primary targets of cybercriminals. They are operating in what can be described as a digital battlefield, where cyber threats are constant and sophisticated.
87% of organizations experienced at least one application security breach in 2025. Attackers are moving faster than ever, with some cyber intrusions executing in minutes rather than days.
Cybercriminals are infiltrating supply chains and weaponizing trusted credentials. They are exploiting unpatched code at a speed and scale that would have been unimaginable a decade ago.
Development teams now have to embed security at every stage of software development and deployment. This article lays out the most current and battle-tested best practice for doing exactly that.
Inside the Modern Cyber Threat Ecosystem
Mission-critical applications are facing an evolving threat environment shaped by three major trends:
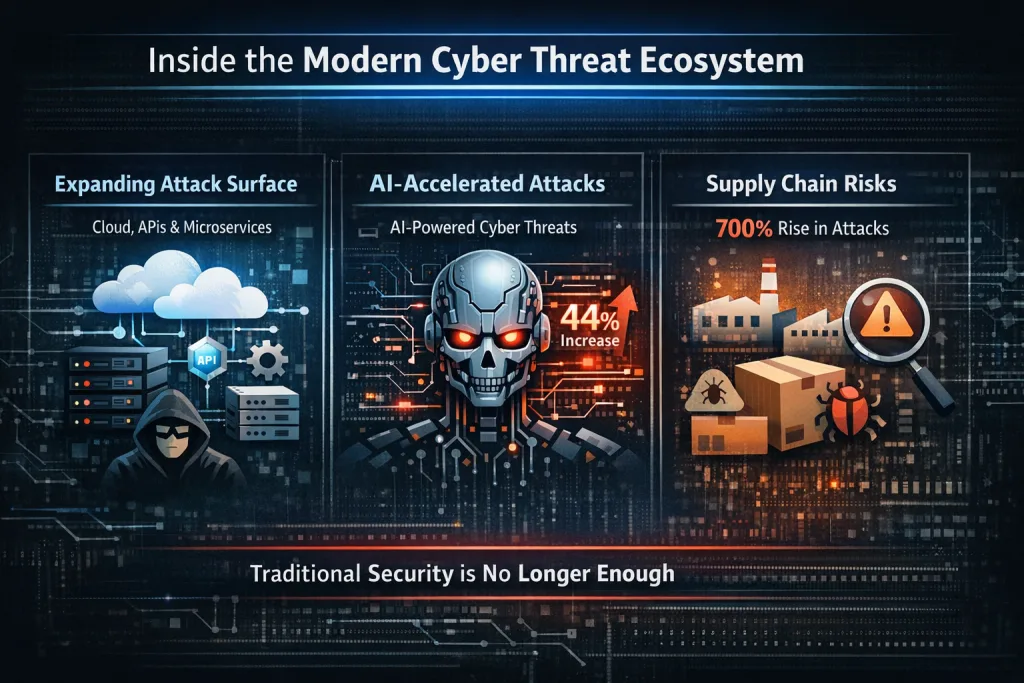
- Expanding Attack Surface: Modern apps rely on cloud infrastructure, APIs, microservices, and third-party integrations. Each component introduces new vulnerabilities and entry points for attackers.
- AI-Accelerated Cyberattacks: Cybercriminals now use AI to exploit vulnerabilities faster and automate attacks. IBM X-Force 2026 report shows a 44% increase in attacks targeting public-facing applications.
- Supply Chain and Dependency Risks: Open-source libraries and third-party components have become essential, but they also introduce hidden vulnerabilities. Supply chain attacks increased by over 700% in recent years.
These realities mean that traditional and reactive security models are no longer sufficient.
Why Mission-Critical Applications Require a Different Security Approach
Mission-critical apps are different from standard applications. They must meet three core requirements:
- Continuous availability (downtime is unacceptable)
- Data integrity (tampering can have severe consequences)
- Operational resilience (systems must function even during attacks)
Failures in these systems can result in financial losses, safety risks, regulatory penalties, or national security implications.
Best Practices for Secure Mission-Critical App Development
Securing mission-critical applications in 2026 requires concrete practices embedded into every layer of the development process.

Adopt a Security-First Architecture from Day Zero
The most expensive mistake in mission-critical development is treating security as a testing-phase concern. Fixing a vulnerability in production costs up to 30 times as much as catching it at design time.
Every project should begin with a formal threat modeling exercise that maps attack surfaces, identifies trust boundaries, data sensitivity, documents data flows, and evaluates compliance needs before a single line of code is written. Every phase (design → development → testing) should include security checkpoints.
Embed Security into Every Stage of the SDLC
The Secure Software Development Lifecycle (SSDLC) treats every stage of software engineering as an opportunity to prevent vulnerabilities. Organizations using this approach spend approximately $227,000 less per breach incident. Some effective practices by stage include:
- Requirements: Define security requirements alongside functional ones.
- Design: Apply least-privilege principles and network segmentation.
- Development: Use SAST tools, secrets detection, dependency scanning, etc.
- Testing: Conduct DAST and penetration testing before every release.
- Post-Deployment: Enforce continuous monitoring and aggressive patch management.
Implement Zero Trust
The perimeter security model is dead. Zero Trust operates on the principle of “never trust, always verify”. For mission-critical applications, this means:
- Mandatory multi-factor authentication across all users and services
- Mutual cryptographic authentication for service-to-service communication
- Granular role-based access controls that minimize blast radius
68% of 2025 breaches involved a human element (phishing, credential misuse, or misconfiguration). Zero Trust is the architectural response to that because it assumes human failure will happen, including ransomware-related credential compromises, and designs so it cannot compound.
Harden the Software Supply Chain
Supply chain breaches almost doubled between 2024 and 2025, which makes vendor security a first-tier concern. The foundation is visibility. Every team needs a complete Software Bill of Materials (SBOM) to know exactly which components live in their production systems.
Beyond that, use package firewalls to block non-compliant dependencies. Also, enforce code signing at every CI/CD pipeline handoff and continuously assess third-party vendors. Assume suppliers will eventually be compromised, and architect systems to maintain integrity when they are.
Automate Security Testing in CI/CD Pipelines
Modern deployment cycles move too fast for manual security review alone. Every code commit should automatically trigger:
- SAST for code-level vulnerability detection
- SCA for open-source dependency risks
- Secrets detection to block credentials from entering version control
- Container image scanning for infrastructure deployments
Failed security gates must block promotion to production. This prevents the accumulation of critical security debt that nearly half of organizations carry today.
Prioritize Cryptographic Integrity and Secure Communications
Sensitive data in transit and at rest must be treated as hostile territory. Baseline requirements include current-standard TLS for all service communication and vault-based secret storage.
For defense, government, and critical infrastructure applications, planning for quantum-resistant cryptography is no longer optional. A formal key management program covering rotation schedules and access controls, along with hardware security modules (HSMs), should be documented and tested well before an incident forces the issue.
Wrapping Up
Secure mission-critical applications aren’t created by adding security later. They are engineered to be secure from the ground up. Systems should be architected to assume a breach, minimize the blast radius, detect quickly, and recover quickly. In short, the digital battlefield is real. The best defense is to design for it deliberately, not discover it reactively.
At Data Pulse Tech, we work with teams to build security into the foundation of their applications, minimizing risks before they ever reach users. Get in touch to explore how a secure development strategy can strengthen your next project.